The gates of a community or of an individual house, are the residents first line of defence. With the number of crimes in today’s world rising exponentially, just having security guards at the gate is insufficient, to say the least. Many gated communities and individual homes are now resorting to the latest technological advancements to secure the gates of their residence. On this front, the technologies in home security have undergone a lot of changes. From basic systems like an alarm ringing if the correct code wasn’t punched in or control panels that only had cryptic codes to systems like Google Home, Apple HomeKit and Amazon Echo, there is now Facial Recognition, CCTVs, Iris Scan and so on. In this article we will learn about some of the latest home security technologies that are being widely used.
1. Face recognition technology
Face recognition is a type of biometric technology that is increasingly becoming a trend in the home security space. With facial recognition systems, technology has taken a leap from sci-fi movies to reality. These systems are capable of verifying the identity of a person and hence deployed in places where security is critical.Facial recognition is a three step process: detection, face-print creation and verification. The system takes an image from an unknown person with a camera (detection), analyses the data (face print creation), and matches them to existing entries in a database of known people’s faces (verification). Various apartments and villas use this technology to make sure that only the authorized people enter the community. Only if a match is found and the person is verified, will they be let into the home or society. Click here to see a video about how face recognition technology works.
Some popular manufactures of this technology are:
- American manufacturers — StoneLock.
- Japanese manufacturers — Ayonix.
- Indian manufacturers — Rohin communication, Delhi
Some of the common advantages of this technology are:
- Increases the security system in the society
- Easy to identify culprits.
- Reduces operational costs.
Some of the common disadvantages of this technology are:
- They are 100% accurate.
- Requires integration/additional hardware equipment.
- Results can be altered if the individual wears glasses, masks, long hair.
- Many consider this technology as an invasion of technology.
2. Iris scan
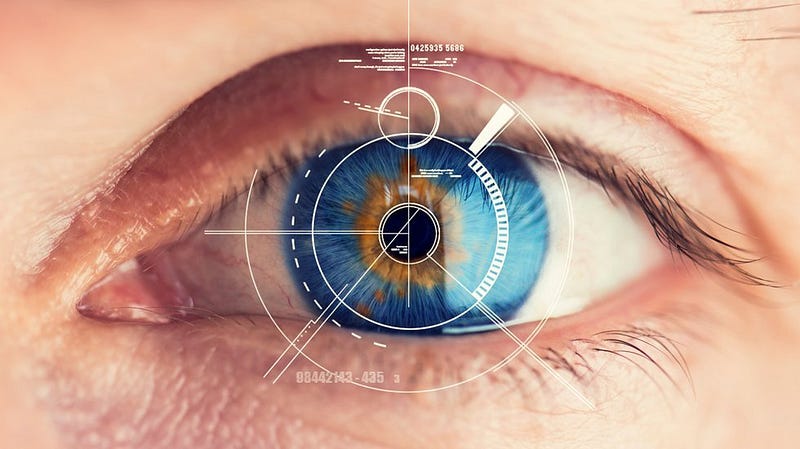
Iris scan recognition is also a biometric identification that uses the unique patterns in the coloured circle of our eyes to identify and validate the visitor’s identity. Many gated communities and independent villas have started using this technology to prevent unwanted people to enter the gates of their society or homes.
There are two stages involved in iris scanning- enrollment and verification. The first time when the person stands in front of a camera their eyes are digitally photographed with two lights, ordinary light and invisible infrared light. The infrared light helps to bring out the unique features of darkly coloured eyes that may not be visible in ordinary light. Once this is done, 240 unique features of every entry are converted into a 512 digit iris code stored along with the name and other essential details in the database. Once this is done, the visitor is enrolled. When he next stands in-front of the camera, the eye is photographed, the image is processed and matched with the earlier stored iris code and so the person is validated.
Some popular manufacturers of this technology are:
- American manufacturers — Iris ID Systems Inc
- Korean manufacturers — CMITECH Co., Ltd
- British technologies — Sensor Access Technology
Some of the common advantages of technology are:
- These systems are very accurate.
- The verification time of these machines are generally less than 5 seconds.
Some of the common disadvantages of technology are:
- This technology is very expensive.
- This technology uses a lot of memory to store data.
3. CCTV

CCTV (Closed circuit television) systems have become increasingly popular over the last few decades, since this technology is reliable and affordable. This technology is generally used for surveillance and security purposes and is used in most banks, apartments and villas. CCTV camera, unlike any other video camera, comes with a monitor and is also capable of wirelessly transmitting images to the monitor. After the monitor has received the images, they are sent to the video tape or DVR (Digital video recorder).In the gated communities and individual villas, this technology is generally used to keep a check of every person who steps in and out of the gates. It also helps to trace the culprit, in case of a mishap, by replaying the tape of the DVD.
Some of the popular Indian manufacturers are:
- Hikvision
- Zicom
- AV Systems
Some of the common advantages of this technology:
- It keeps a track on the culprits action.
- It acts as a legal proof of the past events.
- Helps taking logical decisions.
Some of the common disadvantages of this technology:
- The equipment has additional hardware/ maintenance costs.
- It is pretty expensive.
- Once broken, the entire equipment has to be replaced.
4.Fingerprint Biometric

Fingerprint biometrics is an electronic method of validating a person’s identity, by authenticating his/her fingerprint. The person places his/her finger on the biometric device and if the fingerprint matches with the records in the database, their identity is validated and they gain entry. Fingerprint biometrics, in most cases, is used to make sure that the problem of proxies/im-personification is eliminated.
